I have a hard time gathering all the mup knowledge honestly. But it appears that mup can create a docker swarm. There, you can add a service similar to this to just “enable” traefik, and remove the nginx proxy.
version: '3'
services:
loadbalancer:
image: traefik:alpine
command: |
--docker \
--entryPoints="Name:http Address::80 Redirect.EntryPoint:https" \
--entryPoints="Name:https Address::443 TLS" \
--retry \
--acme \
--acme.tlschallenge \
--acme.email="youremail@example.com" \
--acme.storage="/data/acme.json" \
--acme.entrypoint="https" \
--acme.ondemand=true \
--docker.swarmmode \
--docker.watch \
--docker.exposedbydefault=false
ports:
- 80:80
- 443:443
volumes:
- /var/run/docker.sock:/var/run/docker.sock
- loadbalancerdata:/data
deploy:
restart_policy:
condition: on-failure
window: 8s
volumes:
loadbalancerdata:
Then, the labels you have to instruct mup to add to your nodes are:
"traefik.frontend.rule=Host:your.domainname.com"
"traefik.frontend.entryPoints=http,https"
"traefik.backend.loadbalancer.swarm=true"
"traefik.backend.loadbalancer.stickiness=true"
"traefik.port=3000"
"traefik.enable=true"
You can also configure a standalone traefik to run on your host (as opposed to inside docker). Remove all the associated docker configuration from its command line, while keeping stuff like the acme commands. Then, add a config.toml that tells traefik about your one backend, the exposed port 80 on your host (i.e., docker swarm exposing port 80 and load balancing, randomly, among all hosts).
I’ll be honest and say that while mup is maintained, it doesn’t really make sense. Architecturally, it is equivalent to a bash script that scpes your settings.json onto the remote host, sshes into a remote host, runs git pull on your project repository, runs the meteor build process, kill -2 any existing node processes, and then calls node main.js in your bundle. Considering that nearly everyone is using it on Ubuntu-based cloud hosts, it’s a project will an awful lot of obscurity and GitHub Issues for something as (relatively!) straightforward as running a process.
docker provides a decent, if complicated, way to call node main.js multiple times, much like foreman does; and traefik provides a decent, if complicated, way to sticky-sessions route web requests and handle SSL conveniently to these multiple processes disguised as docker containers. It took me about a day to learn how to write a docker-compose.yml, compatible with docker swarm, that includes traefik and my docker image containing my meteor application, to deploy everything in a less obscure way.
However, if mup is working for you, and you’re dead set on not doing any of this stuff, then I suppose you’re going to have to deal with these mysterious issues. But then again, we don’t actually know if they’re related!
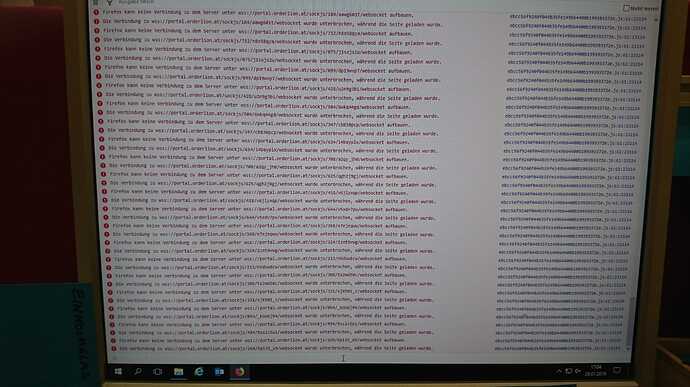
I should remind you that I could be totally wrong. Your SSL problems may be unrelated to anything we’ve talked about. All I’m saying is that the node ecosystem is complex, and I don’t think Galaxy (or anything the meteor devs test with) has this issue, and Galaxy doesn’t use mup.